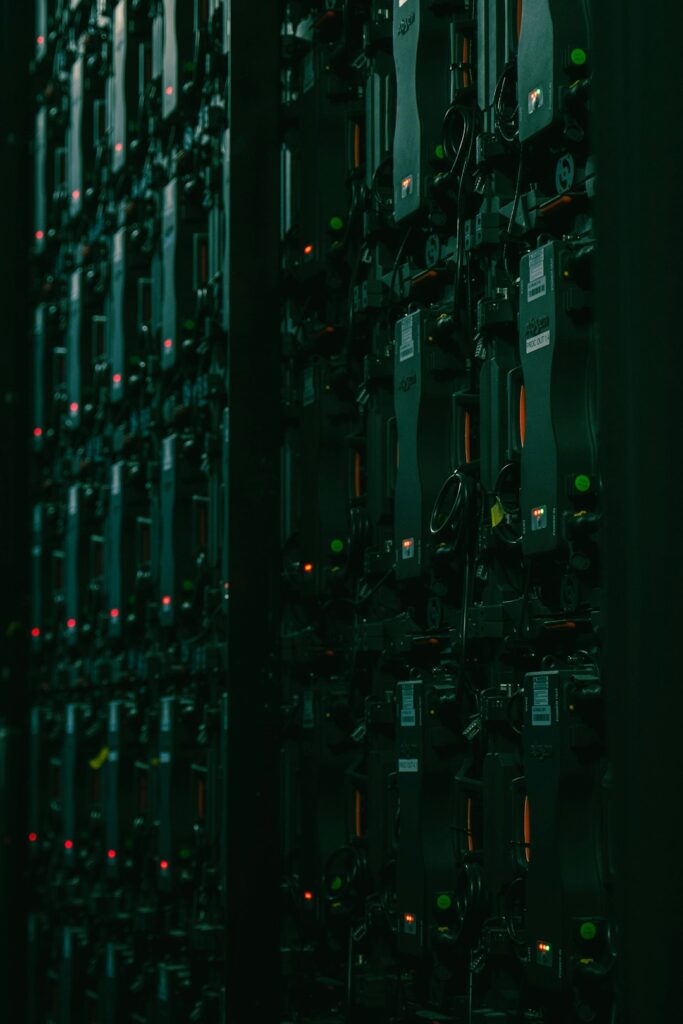
How Is Your Cloud Security Configured?
Running an online store means dealing with sensitive customer data every day. Yet, a common mistake is trusting that moving to the cloud automatically secures that data. It doesn’t. Cloud providers do offer baseline protections, but the security of your platform depends heavily on how you set it up. For instance, many retailers overlook the importance of tightly controlled user permissions on their B2C Commerce Cloud environments. If access isn’t restricted properly, unauthorized users might gain entry to personal or payment information, creating serious risks for data breaches and damaging your reputation. There’s a widespread misconception that using cloud services means you’re automatically compliant with standards like PCI DSS. Compliance, however, demands continuous attention. Companies must regularly review their security settings and perform audits to ensure controls remain effective. One practical step is maintaining a detailed log of configuration changes, which helps track who made updates and when. This record is invaluable during compliance assessments and troubleshooting security incidents. Automated tools designed to scan cloud configurations can catch vulnerabilities early. These systems monitor for issues like overly broad permissions or exposed storage buckets that could lead to data leaks. They provide alerts in real time, allowing teams to react quickly before attackers exploit weaknesses. Integrating such monitoring with Cloud Security Configuration tools brings clarity to what can otherwise be a confusing patchwork of settings across different cloud services. Layered defenses are necessary. Firewalls alone won’t stop every threat. Combining intrusion detection systems with encryption protocols for data at rest and in transit adds multiple hurdles for potential intruders. Many organizations also use network segmentation to limit the scope of any breach, isolating sensitive systems from less critical ones. This kind of multi-tier protection reduces risk and reassures customers that their data is handled seriously. Consider a children’s clothing brand that suffered a major breach after failing to monitor access controls properly. The fallout included lost sales and a damaged brand image that took years to repair. If they had adopted fraud prevention techniques for online retailers early, many issues might have been avoided. This example shows that cloud security configuration isn’t just about meeting rules; it’s about preventing real financial and reputational harm. Regular training for staff managing cloud environments is often neglected but critical. Miscommunication about roles or responsibilities can leave gaps that attackers exploit. Setting up clear procedures for updating configurations and verifying changes through peer reviews can catch mistakes before they reach production. In practice, teams often keep a shared document outlining current security policies, which helps prevent confusion and ensures everyone follows the same standards. Security threats evolve constantly as new vulnerabilities emerge with software updates and new technologies. Staying informed means subscribing to security bulletins from trusted industry sources and participating in relevant forums or webinars. This proactive approach helps businesses spot emerging risks early and adapt their cloud security configurations accordingly, rather than reacting after an incident has occurred. Additionally, companies should consider implementing regular penetration testing to identify potential weaknesses before attackers do. This proactive measure complements automated scanning tools and manual audits, providing a comprehensive view of security posture. Furthermore, adopting a zero-trust model can enhance protection by verifying every access attempt regardless of origin. Another important aspect is data backup and recovery planning. Ensuring that backups are encrypted and stored securely offsite can mitigate the impact of ransomware attacks or accidental data loss. Regularly testing recovery procedures guarantees that businesses can restore operations swiftly in case of an incident. Finally, fostering a culture of security awareness among all employees is crucial. Phishing attacks and social engineering remain common vectors for breaches. Training staff to recognize and report suspicious activities helps create an additional layer of defense, reducing the likelihood of successful attacks.